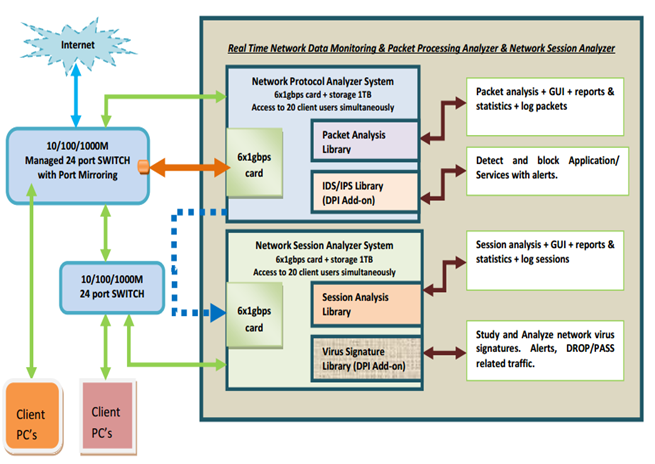
Monosek is a Network Packet Processing and Network Session Analysis System. It offers the most complex packet and flow processing with L2-L4 packet processing, L4-L7 flow processing.
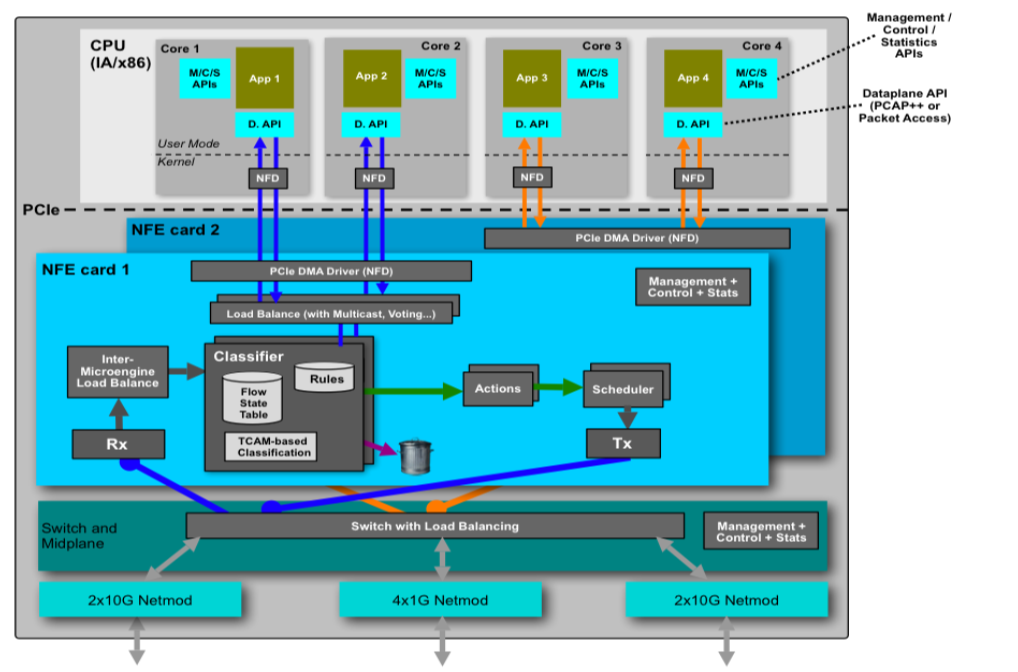
This architecture has three layers of workload-specific packet, flow, security and application processing, each with increasing levels of granularity.
The software modules are available for Packet Analysis, Session Analysis with Deep Packet Inspection Library Interface and Flow analysis.